Last week, Tidelift CEO and co-founder Donald Fischer hosted a webinar where he analyzed the new government cybersecurity regulations to help organizations building applications with open source understand how they may be impacted. Below are some of the highlights and to hear the whole story, you can watch the webinar on-demand now.
How did we get here?
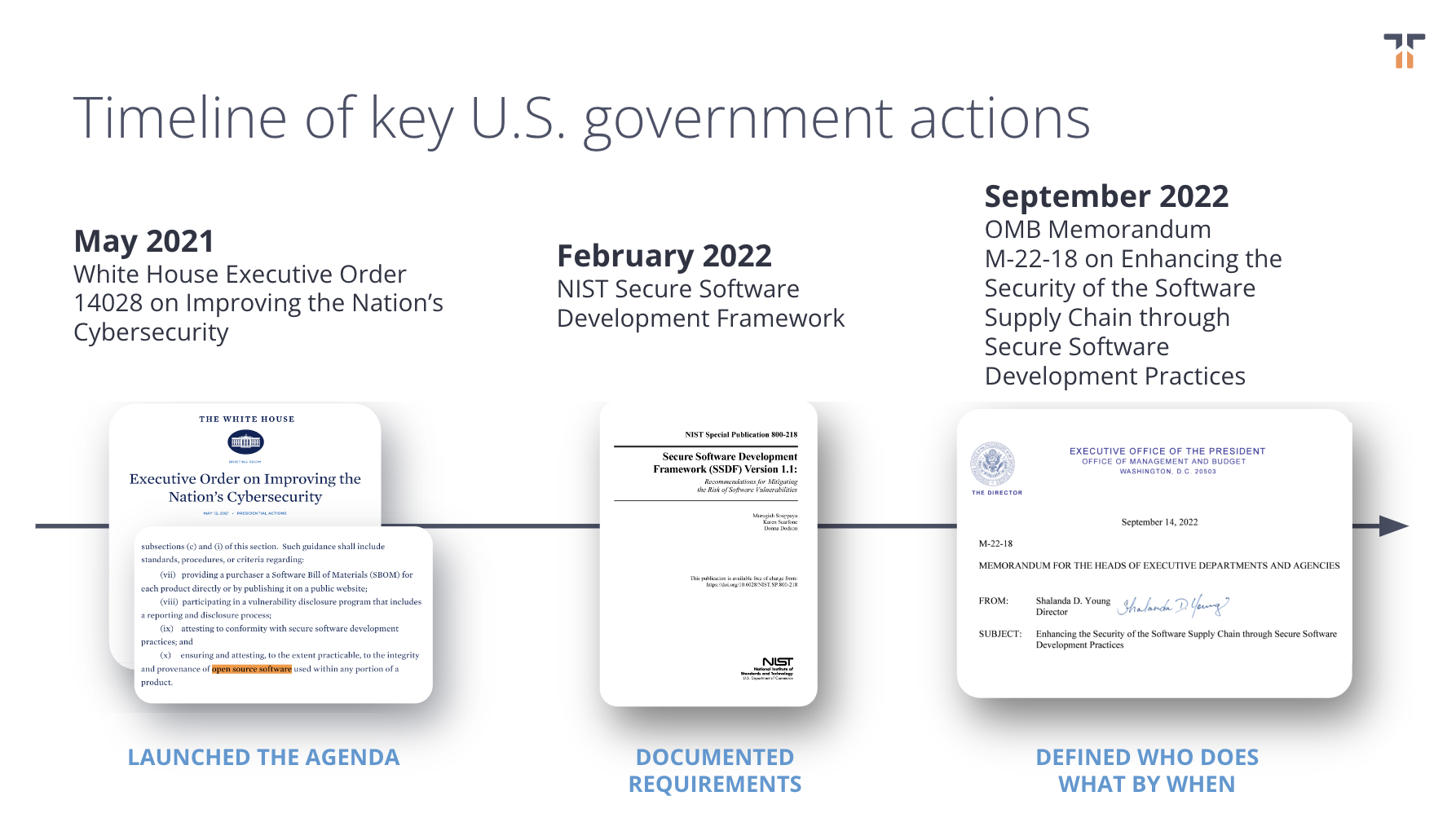
Donald kicked off the webinar by offering a bit of context as to how these U.S. government requirements came into being. In the last decade we’ve seen cybersecurity events such as Heartbleed, the Equifax and Apache Struts incident, the SolarWinds breach, and most recently the Log4Shell supply chain vulnerability—and the U.S. government has taken notice.

In response to the growing number of cybersecurity issues, the U.S. government (and other governments around the world, including the EU) started publicly announcing initiatives and guidelines to improve cybersecurity.
In May 2021, The White House issued Executive Order 14028 on Improving the Nation’s cybersecurity and following directives from Executive Order 14028, the National Institute of Standards and Technology (NIST) published specific guidance on secure software development standards (including for third-party software) in its NIST Secure Software Development Framework and NIST Software Supply Chain Security Guidance documents. Next, came White House Office of Management and Budget (OMB) memorandum M-22-18, which stated that organizations will need to self-attest that they comply with all the proposed NIST guidelines by as soon as June 2023, among other key deadlines.
What is self-attestation?
Attestation is the “issue of a statement, based on a decision, that fulfillment of specified requirements has been demonstrated.” In this case, organizations selling software to the government will be required to self-attest that they conform with all of the secure software development standards outlined in the NIST guidelines.
Source: Software Supply Chain Security Guidance Under Executive Order (EO) 14028 Section 4e
For more information on self-attestation and the associated key dates, we recommend reading our blog post breaking down upcoming deadlines.
It’s important to note that self-attestation will likely include attesting to the security practices of the open source being used in an organization’s applications, so organizations using open source should be paying particular attention to these new requirements as they continue to become more clear.
What organizations will be impacted by these new requirements?
Donald shared a chart showing how these new requirements will in some way impact all organizations.
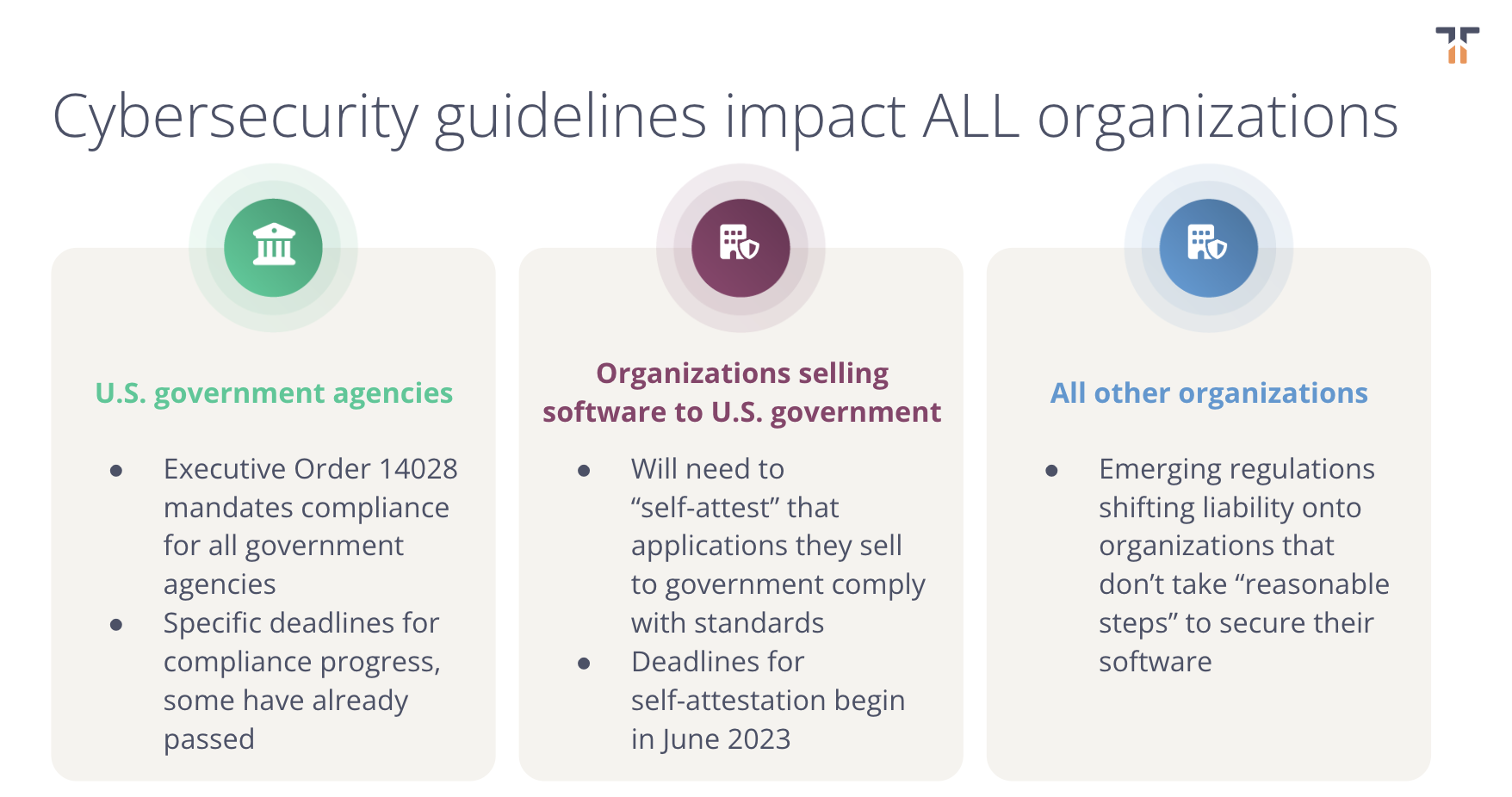
- U.S. government agencies are already seeing direct impacts, and have specific deadlines around compliance under Executive Order 14028 and OMB Memorandum M-22-18.
- But any organization selling software to the government will want to pay close attention to how the self-attestation requirements impact them, as some of these deadlines are now only months away.
- Even organizations that do not do business with the U.S. government directly will want to understand how the new U.S. government cybersecurity policies will impact them, with the government attempting to shift liability onto organizations that don’t take reasonable steps to secure their software. (See the $700m in fines the FTC levied on Equifax after its failure to patch a vulnerability in the Apache Struts open source project caused the leak of millions of sensitive consumer data records for one notable example of where this has already happened).
What questions should your organization be asking?
Donald recommended that technology leaders should start asking themselves some simple questions to get their arms around the impact that these new cybersecurity regulations will have on their work. Organizations that sell software to the government may want to start here:
- Are we using open source components in the applications we provide to the government today?
- If so, how do we plan to attest to the security practices followed by the independent open source maintainers of these components?
- If we consider open source a critical component in our software supply chain, what is our business / contractual relationship with maintainers, i.e. why should they do this security work for us?
- If we do not have an open source self-attestation strategy, how will we comply with new government guidelines?
To answer these questions and to implement a self-attestation gameplan, organizations will need to have visibility into their open source software supply chain to understand more about the components they are using and the security practices these projects follow.
Yet, the so-called open source software supply chain is not a traditional supply chain in that open source maintainers typically do not have a business relationship with their users and license their software “as-is” with no warranty (see our blog post Oops! I’m part of a supply chain! for more info.). It’s more important now than ever to work alongside open source maintainers to improve the security of the software supply chain upstream.
Tidelift partners directly with maintainers to ensure their projects meet critical government and industry standards, and we pay maintainers for this important work. To learn more about the government guidelines outlined above and to figure out how your organization can be prepared for the upcoming deadlines, you can watch the webinar here or visit our government open source cybersecurity resource center.



 50 Milk St, 16th Floor, Boston, MA 02109
50 Milk St, 16th Floor, Boston, MA 02109